France is once again locked in a political fight over encrypted chats. In a May 2026 statement, the French Parliament’s intelligence delegation portrayed secure messengers as an obstacle for police, prosecutors and intelligence services, while acknowledging that end-to-end encryption has become the norm for much digital communication. Users have gained a powerful layer of security and privacy. Investigators, however, still regard unreadable content as a central problem. The debate that gripped France in 2025 has now returned, with implications reaching far beyond Paris.
At stake is whether the state should be allowed to force providers such as Signal, WhatsApp and other messengers to make protected messages accessible under certain conditions. Supporters call it targeted and controlled access. Critics call it a backdoor that weakens protection for everyone.
The shift in language matters. Hardly any politician openly demands insecure communication. Instead, the talk is of technical cooperation, certified solutions and narrow legal safeguards. For cryptographers, the substance is unchanged. Building third-party access into an end-to-end encrypted system fundamentally alters its security promise.
Lawmakers Demand the Impossible
The French delegation is trying to resolve precisely that contradiction. It argues that targeted access to selected encrypted content could be possible without lowering the general level of security. Yet the same body also criticizes a protective clause discussed in another legislative context. In France’s bill on the resilience of critical infrastructure, lawmakers considered an article designed to ensure that providers of encryption services could not be forced to build in technical weaknesses. The provision was intended to ban master keys and other mechanisms that allow protected data to be accessed without the user’s consent.
The parliamentary body now warns that such a rule could endanger intelligence policy and signal to platforms that secure encryption is acceptable. In effect, lawmakers are objecting to a legal safeguard designed to limit the reach of intelligence services.
The conflict has a history. In March 2025, the French National Assembly debated a controversial section of a bill against drug trafficking. Article 8 would have required encrypted messengers to hand over content to investigators, even when messages were protected by end-to-end encryption.
Le Monde reported at the time that the provision would in practice have forced providers such as WhatsApp and Signal to create ways to decrypt messages or make them readable. Then Interior Minister Bruno Retailleau backed the measure and denied that it amounted to a backdoor. Experts disagreed and regarded it as exactly that kind of weakness.
A Victory for Cryptography
In the end, the most sensitive part of the 2025 proposal was stopped in the National Assembly. The Electronic Frontier Foundation described the rejection as a victory for encryption and digital security. Yet the latest move shows that the idea has not disappeared. It has merely returned in another form. At times the justification is drug smuggling, at others terrorism, espionage, foreign influence or the resilience of critical infrastructure. The political pattern remains familiar. Encryption is described as a shield for citizens, but also as a tool for criminals and enemies of the state.
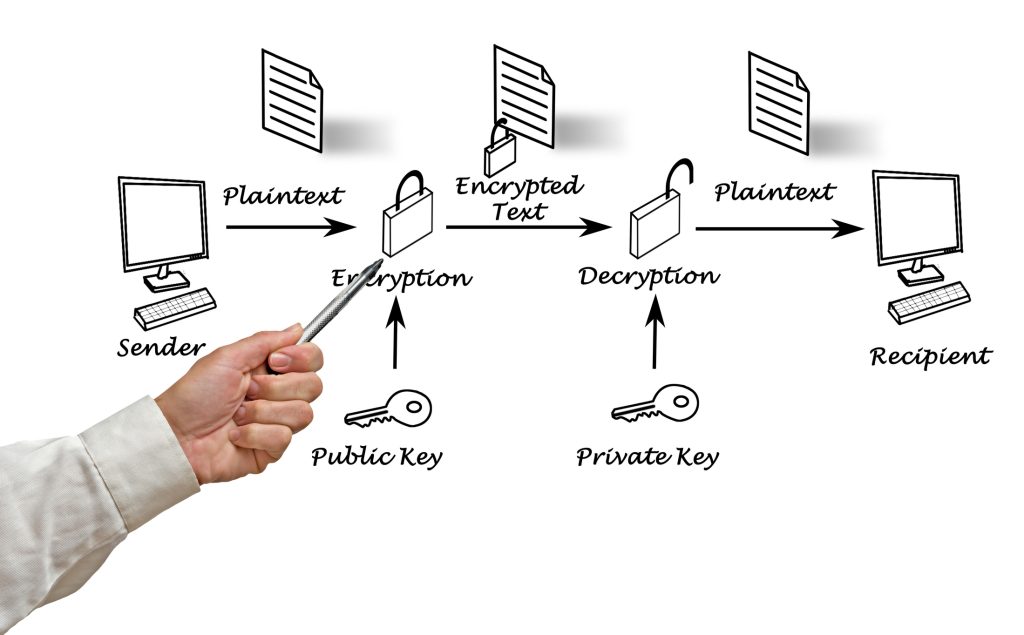
Technically, the problem is simple. End-to-end encryption means that only the sender and the recipient can read the content. The service provider has no key that would allow it to open a conversation later. A demand for exclusive official access undermines that principle. Any deliberately built-in weakness could later be exploited by criminals, foreign intelligence services or hackers.
That is where the political demand collides with technical reality. Access “only for the good guys” cannot be reliably guaranteed.
Pressure Is Growing Across Europe
Pressure on secure messaging has also increased at the European level. In 2024, Europol and the police chiefs of several European states called for ways to bypass messenger encryption during investigations. Security experts countered that weakening it would not only affect suspects. It would expose all users, including journalists, lawyers, companies, activists and state bodies themselves.
The legal position is also fraught. In Podchasov v Russia, the European Court of Human Rights ruled that weakening end-to-end encryption can lead to general and indiscriminate surveillance and violate the right to respect for private life. The case concerned Telegram and Russian demands for decryption keys. The authors of the statement may believe that a targeted model could be compatible with such requirements. They have yet to show how abuse could be prevented.
Political distrust has also been reinforced by France’s handling of Telegram.
Fundamental Digital Trust Is at Risk
After the arrest of Telegram founder Pavel Durov, Axios reported that French authorities had referred, among other things, to older obligations requiring the declaration of encryption technology. Civil rights organizations saw the move as a sign that France views encryption itself with suspicion.
An older case shows how politically sensitive the technology can be. Phil Zimmermann, the inventor of Pretty Good Privacy (PGP), faced a three-year investigation by US customs authorities after PGP began spreading around the world as freeware on the internet in 1991. When used correctly, PGP cannot be compromised. The US government argued that American export restrictions on cryptographic software had been violated once the program became freely available.
The new French debate is therefore more than a dispute over messengers. It concerns the foundation of digital confidentiality. States have legitimate security interests, and investigators need effective tools to fight serious crime. But a society that weakens secure communication pays a high price.
Encryption does not only protect suspects. It protects banking, health data, family conversations, trade secrets and political opposition. France is again looking for a middle path that does not exist in technical terms.
Corrupted encryption is no longer encryption.